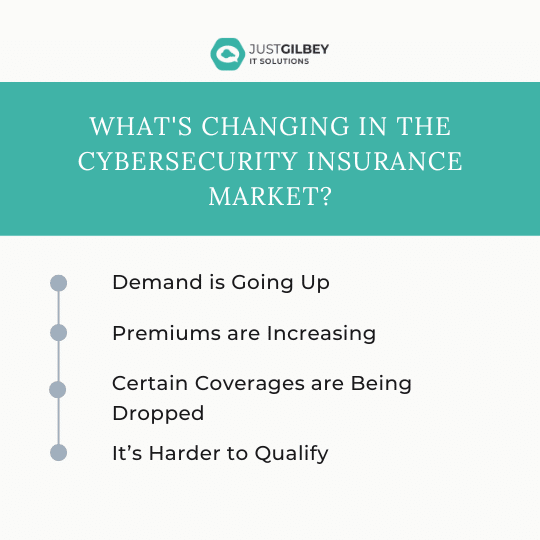
What’s Changing in the Cybersecurity Insurance Market?
Cybersecurity insurance is still a pretty new concept for many SMBs. It was initially introduced in the 1990s to provide coverage for large enterprises. It…
What Cybersecurity Attack Trends Should You Watch Out for in 2023?
The new year has just begun and it’s a time of renewal as we plan for the possibilities to come in 2023. It’s also a…
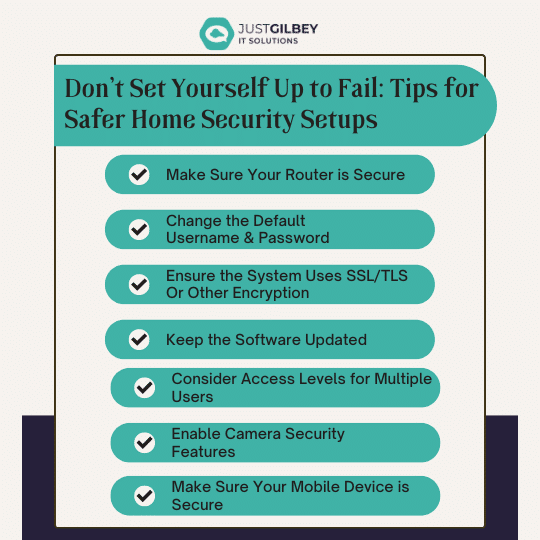
Don’t Set Yourself Up to Fail: Tips for Safer Home Security Setups
The global home security market has been growing by leaps and bounds. By 2026, experts expect the market to expand at a rate of 20.1%….
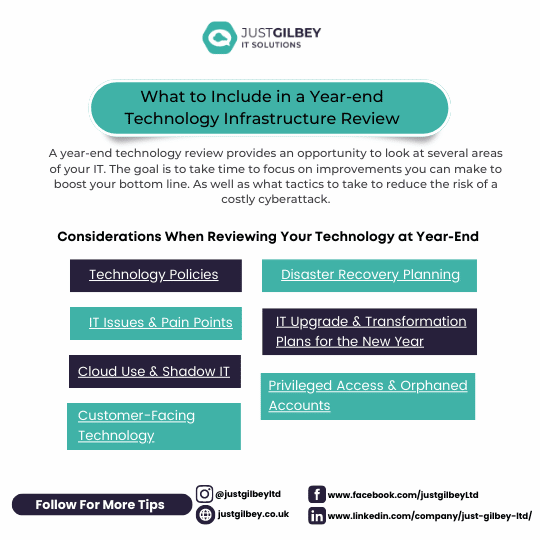
What to Include in a Year-end Technology Infrastructure Review
When the year is coming to a close, it’s the perfect time to plan for the future. Most businesses begin the year with the hope…
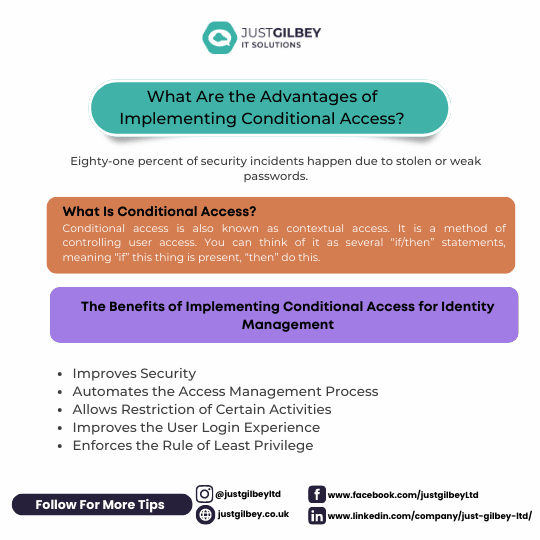
What Are the Advantages of Implementing Conditional Access?
It seems that nearly as long as passwords have been around, they’ve been a major source of security concern. Eighty-one percent of security incidents happen…
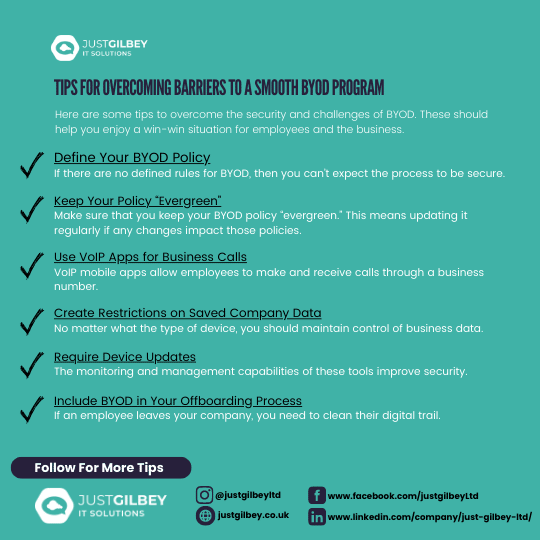
Tips for Overcoming Barriers to a Smooth BYOD Program
Bring your own device (BYOD) is a concept that took hold after the invention of the smartphone. When phones got smarter, software developers began creating…
Simple Setup Checklist for Microsoft Teams
Microsoft Teams is a lot of things. It’s a video conferencing tool, a team messaging channel, and a tool for in-app co-authoring, just to name…
7 Things to Consider When Getting a New Computer to Avoid Buyer’s Remorse
Have you ever bought a new computer and then had buyer’s remorse a few months later? Maybe you didn’t pay attention to the storage capacity…
7 tips – How to Create an Effective Data Backup Strategy (and Why You Should)
Whether you’re a start-up or global corporation, backups are an essential part of any business’ IT strategy.Making and securing multiple versions of your important data…
7 Apps That Can Help You Improve Customer Experience in 2023
Paying attention to your customer experience directly impacts your bottom line. Companies that are “customer-centric” are 60% more profitable than those that aren’t. In this…